
Apple has always had growing concerns about the safety of users and their equipment. The Find My Phone or data encryption that applies on the iPhone and iPad are just two examples of success that has , among many other techniques and services you use . But Apple wants to go even further and preparing to gather information on the attempts of unauthorized access to their equipment. The patent presented now describes , in detail , various scenarios in which this collection can be made and various types of data that can be collected.
How it will be used the system from Apple ?
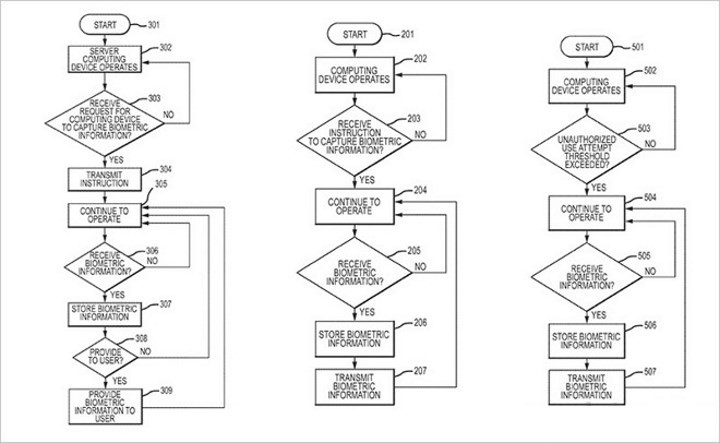
Everything starts with the detection of unauthorized access attempts to a device , when the Touch ID and the camera are used , collecting the fingerprint and photograph of the person who is trying to use . Several other sensors can be used , also being able to collect audio, location, travel speed and data from many other sensors.
Where do data collected by Apple go ?
The patent describes several possible scenarios presented , but the destination of the data should be a two . Or are stored in the machine until it is recovered or are sent to a central server. This second scenario can he show two distinct options. Or the data is also simply stored or are sent to the authorities so that they can then be used as evidence if necessary . Apple has one last chance , that these data are validated against a database authorized users , which will lead to this case is disposed of .

The Apple patent seems to be the ideal process for security reinforcement without the attackers know they are being watched , being simple to implement and complement some offers which currently already exist. Apple has the advantage of having direct access to the fingerprint reader , getting only information about the attacker . There is, however , a legal issue to be addressed and solved before this innovation is released. The collection of biometric data will raise privacy issues that can be difficult to get around . Even if not implementing this system , something that happens repeatedly , the idea is very interesting in itself , leading to potential attackers and identifying new heights.
Thank you so much for being here
Like always see you next time
Gaming&Tech
No comments:
Post a Comment